Your smartphone holds more of your life than you probably realize. From banking apps and private messages to photos, passwords, and even work files, it all sits behind one simple lock screen. This issue highlights how quickly access can be gained. In most cases, these types of vulnerabilities require physical access to the device, but that does not make them harmless. Think about how often you leave your phone unattended, even for a moment. A quick stop at a café, a phone left on a desk, or even a misplaced device at home could create an opening.
But not every Android phone is at risk in the same way, and not every device can be unlocked instantly. However, the situation does raise a bigger question. If someone had your phone for just one minute, what could they actually do?
If Someone Had Your Phone for Just 60 Seconds
Imagine you set your phone down on a table while grabbing a coffee. Or maybe you hand it to someone briefly, without thinking twice. It feels harmless. After all, it is just a minute. Now consider what that minute could allow.

With the right exploit, a person could bypass certain lock screen protections and gain access to the device. While this does not apply to every phone or every Android version, it has been demonstrated in specific cases involving software flaws. These flaws can sometimes be triggered through unusual inputs or system loopholes that were never meant to be used that way.
Once inside, the clock starts ticking.
Access to Messages and Personal Conversations
The first thing someone might check is your messages. Text messages, messaging apps, and even archived chats can reveal a surprising amount of personal detail. Conversations often include sensitive information, from login codes to private discussions. Even if the attacker only scans through your phone, they could gather enough context to attempt further access elsewhere.
Email and Account Recovery Gateways
Next, email becomes a major target. Many accounts rely on email for password resets. If someone can open your inbox, they can potentially:
- Request password resets
- Confirm verification links
- Take control of other accounts tied to that email
In just a few taps, that one unlocked device can become a gateway to a much larger digital footprint.
Saved Passwords and Autofill Data
Many Android users rely on autofill features to save time. While convenient, these tools can also expose stored credentials if the device is compromised. Depending on settings, an attacker might gain access to:
- Website logins
- App credentials
- Payment information
Some systems require additional authentication, which helps. However, not all users enable these protections.

Photos, Files, and Private Data
Photos often feel harmless, but they can contain more information than expected. Location data, personal moments, and even documents stored as images can all be accessed quickly.
Beyond that, file storage apps may hold:
- Work documents
- IDs or personal records
- Downloaded files with sensitive details
It does not take long to scroll, screenshot, or transfer key pieces of information.
Apps That Stay Logged In
Many apps keep users logged in for convenience. Banking apps, shopping platforms, and social media accounts often open instantly once the phone is unlocked. While some banking apps require extra verification, others rely on device-level security. If that is bypassed, the protection weakens.
From there, actions could include:
- Viewing account balances
- Making purchases
- Sending messages from your accounts
Even if the attacker does not complete a transaction, they may gather enough data to attempt one later.

This is not about creating panic. Rather, it is about awareness. Most people assume their lock screen is an unbreakable barrier. But it’s just one step in a broader system. And when that fails, even briefly, the impact can extend far beyond the device itself.
How This Android Vulnerability Actually Works
While the idea of someone unlocking your phone in under a minute sounds scary, the mechanics behind it are often more technical than the headlines suggest. In most reported cases, these vulnerabilities are not universal flaws that affect every device in the same way. Instead, they tend to appear in specific versions of Android, often tied to how the lock screen interacts with other system features.
For example, some exploits rely on triggering unusual behavior through repeated inputs or by overwhelming certain parts of the interface. In past cases, attackers have used things like camera access, emergency dialers, or notification previews to create small cracks in the system. These cracks do not immediately unlock the phone, but they can sometimes be manipulated to bypass the lock screen entirely. Once that happens, the device may briefly grant access to areas that should remain protected.
What makes this possible is not a single mistake, but a combination of small oversights. Software is incredibly complex, and even well-tested systems can have edge cases that developers did not anticipate. When those edge cases are discovered, they can be turned into exploit paths. That said, these methods usually require very specific steps. They are not as simple as pressing a button or running a basic app. In many situations, the attacker needs to understand the exact sequence needed to trigger the flaw.
These vulnerabilities are often patched quickly once identified. Google releases regular security updates for Android, and manufacturers push those updates to users as they become available. The real issue arises when devices do not receive updates consistently, or when users delay installing them. In those cases, the window of exposure stays open longer than it should.
Why Outdated Devices Face the Greatest Risk
One of the most important factors in this entire situation is not the vulnerability itself, but how long it remains unpatched on real devices. In theory, once a flaw is discovered, it should be fixed quickly. In practice, that process can take time, and not all devices receive updates at the same pace.
Android operates across a wide range of manufacturers, each with its own update schedule. Some brands push updates regularly, while others lag behind. Older devices often stop receiving updates altogether, leaving them permanently exposed to known vulnerabilities.
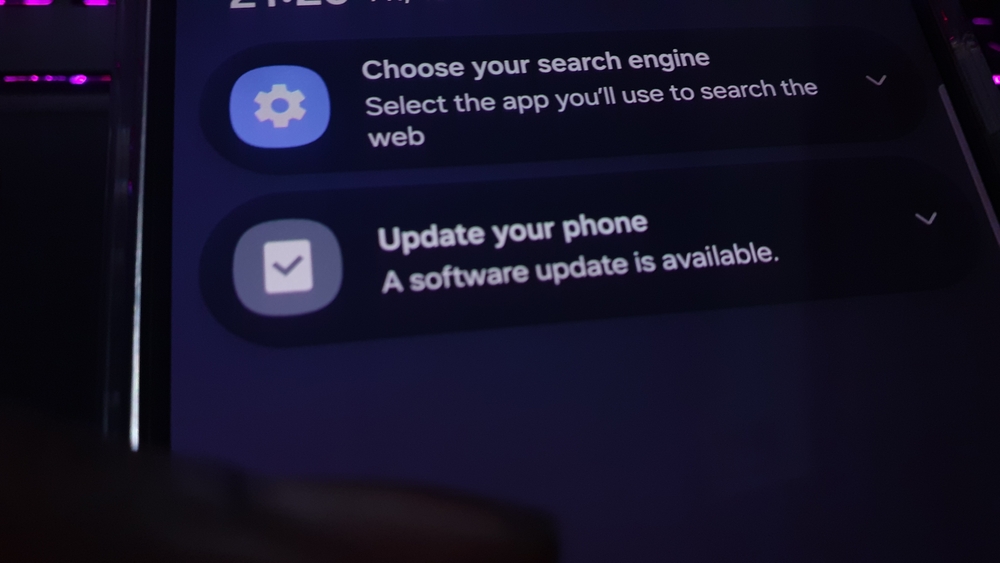
Many people also ignore update notifications. It is easy to postpone an update, especially when it seems inconvenient. However, those updates often contain critical security patches. Skipping them means continuing to use a device with known weaknesses.
Another thing to consider is how long people keep their phones. Unlike laptops or other devices, smartphones are often used for several years. As they age, they fall further behind in terms of security support. This makes them more attractive targets, not because they are inherently weaker, but because they are no longer being actively protected.
How to Check If Your Device Is Affected
If you want to find out if this vulnerability applies to your phone, there are a few simple steps you can take. Start by identifying your device’s chipset, also known as the SoC (system on a chip). You can usually find this information by searching your phone model on sites like GSMArena or checking your manufacturer’s official website.
Once you have that detail, the next step is to compare it against the list of affected chipsets in MediaTek’s March security bulletin. Specifically, look for the entry labeled CVE-2026-20435, which outlines the vulnerability in question. MediaTek provides a public security page where you can review this information and confirm whether your device may be impacted.
This process might sound a bit technical, but it only takes a few minutes. More importantly, it gives you a clearer picture of your actual risk, rather than relying on general headlines.
The Illusion of Smartphone Security
Most people feel a sense of safety when they lock their phones. Whether it is a fingerprint, facial recognition, or a PIN, these features create the impression that the device is fully protected.
Biometric security, for example, is designed for convenience as much as protection. It allows users to unlock their devices quickly, which improves the overall experience. However, it is not foolproof, and there have been cases where fingerprints can be replicated or facial recognition can be bypassed under certain conditions.
Similarly, many apps rely on the assumption that the device itself is secure. If the lock screen is bypassed, those apps may become more accessible than intended. Some applications add extra protection, such as requiring a password or biometric confirmation before opening. But others don’t, which creates inconsistencies in how secure different parts of the device really are.

This creates what can be described as an illusion of security. Everything feels locked down, but that sense of safety depends on multiple factors working together perfectly. When one thing fails, even briefly, the system becomes more vulnerable than most users expect.
For the average person, these vulnerabilities are unlikely to be exploited in everyday life. However, they do challenge the idea that a locked phone is completely safe.
Convenience vs. Protection in Modern Devices
Modern smartphones are built around speed and ease of use. Every feature is designed to reduce friction, from instant unlocking to saved passwords and automatic logins. When a device unlocks quickly, it improves the user experience. However, it also means that once access is gained, everything else becomes easier to reach. Apps open instantly, accounts stay logged in, and information is readily available. This is ideal for the user, but it can also benefit someone who gains unauthorized access.
Developers constantly balance these competing priorities. Too much security can make a device frustrating to use, but too little security can leave your phone and information exposed. The result is a system that aims to be both secure and convenient, but never perfectly achieves it.
The vulnerabilities of Android show us how complex modern devices have become. Each feature adds value, but also increases the number of potential entry points. For users, this means thinking differently about security. It is not just about setting a lock screen and forgetting about it. It is about understanding how different features interact and where potential gaps might exist. Small changes, such as enabling additional authentication for sensitive apps, can make a difference.

Beyond One Vulnerability
This article isn’t just about hackers or a specific Android flaw. Its about how we think about security in a world where our devices hold so much of our personal information. The idea that someone could gain access in under a minute forces us to rethink things.
A device that feels secure can become vulnerable in a matter of seconds, depending on the circumstances. It also underscores the importance of staying informed about technology and the risks associated with it.
More importantly, it reminds us that security is not a fixed state. It is something that requires ongoing attention. Updates need to be installed, settings need to be reviewed, and habits need to be adjusted over time. While that may sound like extra effort, it is a small price to pay for protecting something as central as your smartphone.
Read More: You Can (and Should) Delete Yourself From The Internet. Here’s How.
It Only Takes a Moment to Rethink Your Security
Security is rarely absolute. It works in layers and depends on both technology and user behavior. When one part weakens, the rest can become more exposed than expected. But this is not a reason to panic or distrust your device entirely. Most modern smartphones, including Android devices, still have strong protections in place. Updates are released regularly, and many vulnerabilities are patched before they ever affect a wide number of users.
The system, for the most part, works. However, it does rely on awareness. Something as simple as installing updates, using stronger authentication methods, or limiting what is accessible from a locked screen can make a real difference. Because if one minute is all it takes under the right conditions, then how we think about those sixty seconds matters more than ever.
A.I. Disclaimer: This article was created with AI assistance and edited by a human for accuracy and clarity.
Read More: Vietnam Closes 86 Million Bank Accounts Over Digital ID Requirements

